64位与Windows内核详解
 发布于2025-09-02 阅读(0)
发布于2025-09-02 阅读(0)
扫一扫,手机访问
继续深入学习《逆向工程核心原理》,本篇笔记聚焦于第五部分:64位 & Windows 内核6。
一、x64
1、x64处理器的变化
- 含有VA的指令大小增加了4个字节
- 虚拟内存从4GB扩大到16GB
- 通用寄存器的数量增加到18个,如下所示:

- 函数调用统一为fastcall,可以传递4个参数,如下所示:

- 栈操作不再使用PUSH/POP命令,而是通过MOV操作寄存器和指定的栈
- 栈帧不再使用RBP,改用RSP
2、PE32+
PE32+是64位PE文件
(1)IMAGE_NT_HEADERS
主要是第三个成员不同——IMAGE_OPTIONAL_HEADER64和IMAGE_OPTIONAL_HEADER32

其中IMAGE_FILE_HEADER主要是Machine值变了,如下图所示:

而IMAGE_OPTIONAL_HEADER变化很大:
- Magic值从010B变为020B,作为识别32位还是64位的标志
- BaseOfData删除了
- ImageBase从DWORD变为ULONGLONG类型
- 与栈和堆有关的字段也变为ULONGLONG类型
(2)IMAGE_THUNK_DATA
大小从4个字节变为8个字节

(3)IMAGE_TLS_DIRECTORY
部分成员是VA值,扩展为8个字节

3、WinDbg基本指令

二、内核6
kernel 6 是vista之后的系统,Win10 是kernel 10。
1、会话
会话:登录后的用户环境,kernel 6引入。
- 系统会话是0,与用户会话隔离(即第一个登录的用户是会话1,而之前是会话0)
- 但是会话1中的进程可以强行终止会话0中的进程
2、DLL注入
原先的用CreateRemoteThread()进行DLL注入的方法无法生效,原因是新增的API,如下:

对此,给出新的InjectDll.exe,代码语言为javascript,运行次数为0:
#include "windows.h"
#include "stdio.h"
#include "tchar.h"
BOOL SetPrivilege(LPCTSTR lpszPrivilege, BOOL bEnablePrivilege) {
TOKEN_PRIVILEGES tp;
HANDLE hToken;
LUID luid;
if( !OpenProcessToken(GetCurrentProcess(),
TOKEN_ADJUST_PRIVILEGES | TOKEN_QUERY,
&hToken) ) {
_tprintf(L"OpenProcessToken error: %u\n", GetLastError());
return FALSE;
}
if( !LookupPrivilegeValue(NULL, lpszPrivilege, &luid) ) {
_tprintf(L"LookupPrivilegeValue error: %u\n", GetLastError() );
return FALSE;
}
tp.PrivilegeCount = 1;
tp.Privileges[0].Luid = luid;
if( bEnablePrivilege )
tp.Privileges[0].Attributes = SE_PRIVILEGE_ENABLED;
else
tp.Privileges[0].Attributes = 0;
if( !AdjustTokenPrivileges(hToken, FALSE, &tp, sizeof(TOKEN_PRIVILEGES), (PTOKEN_PRIVILEGES) NULL, (PDWORD) NULL) ) {
_tprintf(L"AdjustTokenPrivileges error: %u\n", GetLastError() );
return FALSE;
}
if( GetLastError() == ERROR_NOT_ALL_ASSIGNED ) {
_tprintf(L"The token does not have the specified privilege. \n");
return FALSE;
}
return TRUE;
}
typedef DWORD (WINAPI *PFNTCREATETHREADEX)(
PHANDLE ThreadHandle,
ACCESS_MASK DesiredAccess,
LPVOID ObjectAttributes,
HANDLE ProcessHandle,
LPTHREAD_START_ROUTINE lpStartAddress,
LPVOID lpParameter,
BOOL CreateSuspended,
DWORD dwStackSize,
DWORD dw1,
DWORD dw2,
LPVOID Unknown );
BOOL IsVistaOrLater(){
OSVERSIONINFO osvi;
ZeroMemory(&osvi, sizeof(OSVERSIONINFO));
osvi.dwOSVersionInfoSize = sizeof(OSVERSIONINFO);
GetVersionEx(&osvi);
if( osvi.dwMajorVersion >= 6 )
return TRUE;
return FALSE;
}
BOOL MyCreateRemoteThread(HANDLE hProcess, LPTHREAD_START_ROUTINE pThreadProc, LPVOID pRemoteBuf){
HANDLE hThread = NULL;
FARPROC pFunc = NULL;
if( IsVistaOrLater() ) {
pFunc = GetProcAddress(GetModuleHandle(L"ntdll.dll"), "NtCreateThreadEx");
if( pFunc == NULL ) {
printf("MyCreateRemoteThread() : GetProcAddress(\"NtCreateThreadEx\") failed!!! [%d]\n", GetLastError());
return FALSE;
}
((PFNTCREATETHREADEX)pFunc)(&hThread, 0x1FFFFF, NULL, hProcess, pThreadProc, pRemoteBuf, FALSE, NULL, NULL, NULL, NULL);
if( hThread == NULL ) {
printf("MyCreateRemoteThread() : NtCreateThreadEx() failed!!! [%d]\n", GetLastError());
return FALSE;
}
}
else {
hThread = CreateRemoteThread(hProcess, NULL, 0, pThreadProc, pRemoteBuf, 0, NULL);
if( hThread == NULL ) {
printf("MyCreateRemoteThread() : CreateRemoteThread() failed!!! [%d]\n", GetLastError());
return FALSE;
}
}
if( WAIT_FAILED == WaitForSingleObject(hThread, INFINITE) ) {
printf("MyCreateRemoteThread() : WaitForSingleObject() failed!!! [%d]\n", GetLastError());
return FALSE;
}
return TRUE;
}
BOOL InjectDll(DWORD dwPID, char *szDllName){
HANDLE hProcess = NULL;
LPVOID pRemoteBuf = NULL;
FARPROC pThreadProc = NULL;
DWORD dwBufSize = strlen(szDllName)+1;
if ( !(hProcess = OpenProcess(PROCESS_ALL_ACCESS, FALSE, dwPID)) ) {
printf("[ERROR] OpenProcess(%d) failed!!! [%d]\n", dwPID, GetLastError());
return FALSE;
}
pRemoteBuf = VirtualAllocEx(hProcess, NULL, dwBufSize, MEM_COMMIT, PAGE_READWRITE);
WriteProcessMemory(hProcess, pRemoteBuf, (LPVOID)szDllName, dwBufSize, NULL);
pThreadProc = GetProcAddress(GetModuleHandle(L"kernel32.dll"), "LoadLibraryA");
if( !MyCreateRemoteThread(hProcess, (LPTHREAD_START_ROUTINE)pThreadProc, pRemoteBuf) ) {
printf("[ERROR] MyCreateRemoteThread() failed!!!\n");
return FALSE;
}
VirtualFreeEx(hProcess, pRemoteBuf, 0, MEM_RELEASE);
CloseHandle(hProcess);
return TRUE;
}
int main(int argc, char *argv[]){
SetPrivilege(SE_DEBUG_NAME, TRUE);
if( argc != 3 ) {
printf("usage : %s <pid><dll_path>\n", argv[0]);
return 1;
}
if( !InjectDll((DWORD)atoi(argv[1]), argv[2]) ) {
printf("InjectDll() failed!!!\n");
return 1;
}
printf("InjectDll() succeeded!!!\n");
return 0;
}结语
主要是因为本书编写时正值32位向64位过渡的时代,故有此章进行一些区别的介绍。
红客突击队由队长k龙于2019年发起,联合国内多所顶尖高校的研究生成立。成立以来,团队多次参与国际网络安全竞赛并取得优异成绩,积累了丰富的竞赛经验。目前,红客突击队拥有三十多名正式成员及若干预备人员,并下设数支联合分队。红客突击队始终秉持先做人后技术的宗旨,致力于打造国际顶尖的网络安全团队。
免责声明:正软商城发布此文仅为传递信息,不代表正软商城认同其观点或证实其描述。
产品推荐
-

售后无忧
立即购买>- DAEMON Tools Lite 10【序列号终身授权 + 中文版 + Win】
-
¥150.00
office旗舰店
-

售后无忧
立即购买>- DAEMON Tools Ultra 5【序列号终身授权 + 中文版 + Win】
-
¥198.00
office旗舰店
-

售后无忧
立即购买>- DAEMON Tools Pro 8【序列号终身授权 + 中文版 + Win】
-
¥189.00
office旗舰店
-
售后无忧
立即购买>- CorelDRAW X8 简体中文【标准版 + Win】
-
¥1788.00
office旗舰店
-
 正版软件
正版软件
- 次元城app下载的文件在哪-下载文件位置
- 次元城app下载的文件在哪,在软件首页选择想观看的动漫,如《我推的孩子第二季》,进入播放页面,点击简介下方“下载”标识(如图片圈注处)。自由勾选单集或选择“全部下载”,点击“下载队列”进入“我的下载”
- 8小时前 21:12 0
-
 正版软件
正版软件
- samhelper怎么测气密性-samhelper测气密性最简单方法
- 使用 SamHelper 检测手机气密性,需打开软件进入测试页面,启动后双指按压屏幕观察气压数值变化。正常状态下,气压基准值约为 1010 左右,按压时数值应有 3-10 左右的波动 。
- 8小时前 21:09 0
-
 正版软件
正版软件
- 白羊影视app怎么使用-使用指南
- 白羊影视app怎么使用,用户在本站下载安装好软件,点击手机桌面图标,打开app,在首页中点击格式转换的功能,选择你想要转换的格式视频导入软件中,选择要转换的格式,然后点击开始转换。
- 8小时前 21:06 0
-
 正版软件
正版软件
- 白羊影视app怎么投屏-投屏教程
- 白羊影视app怎么投屏,首先用手机打开app,然后找到自己想要观看的视频,然后点击屏幕上面的tv功能,然后就会出现搜索投屏机器的蓝牙地址,点击配对,然后成功以后,即可进行投屏操作。
- 8小时前 21:03 0
-
 正版软件
正版软件
- 叮当魔盒app有什么功能-使用指南
- 叮当魔盒app有什么功能,使用手机号码登陆叮当魔盒app,在APP首页滑动盲盒款式,点击“查看宝贝”可详细查看商品明细和抽取概率,选中一款心仪的盲盒,点击“立即开盒”即可进行抽取。
- 8小时前 21:00 0
最新发布
-
 1
1
- B站免费入口官网-B站在线观看永久畅享
- 217天前
-
 2
2
- 高德地图是哪个国家开发的?
- 273天前
-
 3
3
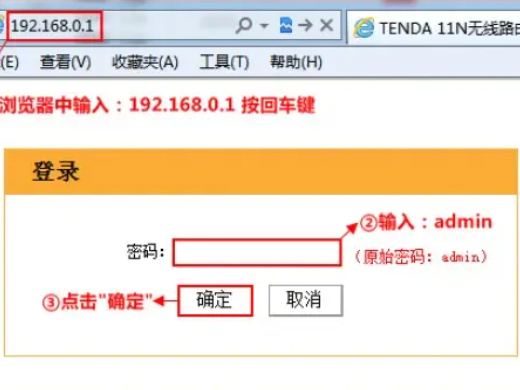
- 如何找到192.168.0.1登录入口
- 326天前
-
 4
4
- 拷贝漫画最新官网入口2025
- 106天前
-
 5
5
- yy漫画下拉式免费阅读官网入口
- 196天前
-
 6
6
- 51漫画高清入口及最新章节更新
- 66天前
-
 7
7
- 2020美团外卖账单报告入口详解
- 215天前
-
 8
8
- 动漫共和国官网入口在线看
- 198天前
-
 9
9
- 抖音去了外地ip多久会变?ip地址怎么变位置?
- 234天前
相关推荐
热门关注
-
- Xshell 6 简体中文
- ¥899.00-¥1149.00
-

- DaVinci Resolve Studio 16 简体中文
- ¥2550.00-¥2550.00
-
- Camtasia 2019 简体中文
- ¥689.00-¥689.00
-

- Luminar 3 简体中文
- ¥288.00-¥288.00
-

- Apowersoft 录屏王 简体中文
- ¥129.00-¥339.00